Early Kaspersky Count Shows Anti-Virus Not Pervasive In Agencies
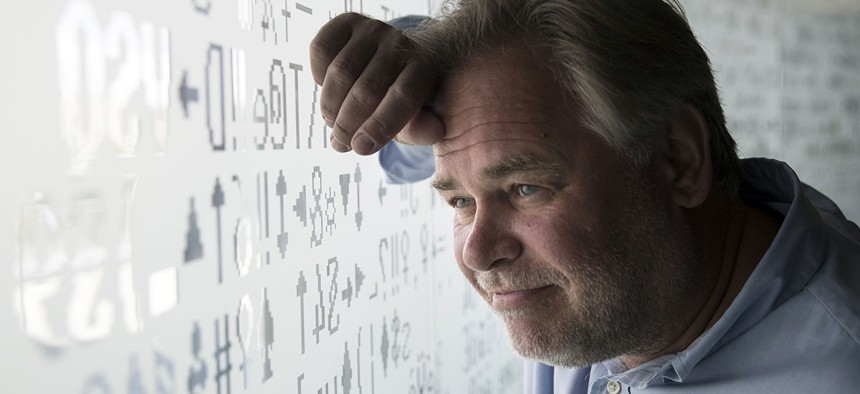
Eugene Kaspersky, Russian antivirus programs developer and chief executive of Russia's Kaspersky Lab, watches trough a window decorated with programming code's symbols at his company's headquarters in Moscow, Russia, Saturday, July 1, 2017. Pavel Golovkin/AP
So far, fewer than half of agencies have reported finding the Russian anti-virus software on their systems, a DHS official said.
The Homeland Security Department has not faced a deluge of Kaspersky instances as federal agencies file their first reports about how widespread the Russian anti-virus software is within government systems, a department official said Friday.
Homeland Security official Michael Duffy confirmed more than half of agencies had met an Oct. 13 deadline to determine if and where the suspect anti-virus was running on their networks, but declined to offer a specific percentage.
Of those that met the deadline, fewer than half found Kaspersky running on any of their systems, Duffy told reporters outside an advisory board meeting.
» Get the best federal technology news and ideas delivered right to your inbox. Sign up here.
Duffy declined to be more specific about the percentage, which could range anywhere from zero to 49 percent.
Homeland Security ordered federal agencies to remove Kaspersky software from all their systems within three months on Sept. 13 following months of suggestions from intelligence officials that the company is tied too closely to the Kremlin.
Kaspersky denies those claims. Colluding with any government’s intelligence service would ruin the company’s business model, officials have said.
Contracting records suggest the spread of Kaspersky in government was substantial but not overwhelming before the ban. Vendors that sell the anti-virus had contracts with the State and Treasury departments among others.
It’s “too soon to tell” whether agencies will meet a December deadline to begin removing Kaspersky from their systems, Duffy said. Removing Kaspersky anti-virus without installing another anti-virus tool could leave agencies more vulnerable rather than more secure, Homeland Security has warned in the past.
Duffy spoke before the National Institute of Standards and Technology’s information security advisory board on the last of three days of meetings.
Here are some other meeting highlights:
- As of last week, there are zero critical software vulnerabilities that have been known but unpatched for more than 30 days on government networks that Homeland Security is monitoring, Duffy said.
- General Services Administration Senior Adviser Eric Mill earlier described the fact some vulnerabilities last as long as 30 days in government as “very problematic.” Reducing maximum patch times well below 30 days should be a major government priority, he said.
- NIST has received 34 submissions so far for a project to build new encryption algorithms that can’t be deciphered by quantum computers, NIST computer security division chief Matthew Scholl said. The institute expects to receive about 50 submissions before a formal deadline in November, he said. The proposals will be part of a years-long process NIST is managing with encryption authorities in numerous nations to strengthen encryption for the quantum computing era.
- NIST is on track to publish a draft report on efforts to combat zombie computer armies known as botnets in November, NIST official Tim Polk said. The institute will seek public feedback on the report, which was required by a May executive order, and combine it with reports being prepared elsewhere in government before delivering it to President Donald Trump in May, he said.



