You Could Win $30K if You Report a Bug in Intel’s Products

ChromaWise/Shutterstock.com
The more severe the flaw, the bigger the pay out.
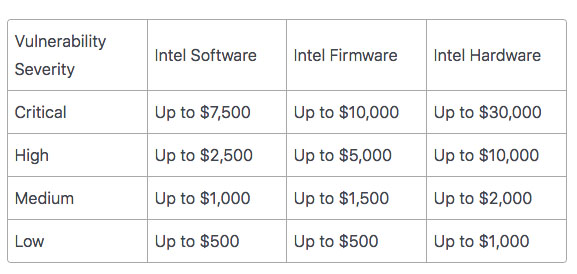
Are you a hacker and want to make some quick cash? Putting your skills to use could net you up to $30,000 if you find and report a “critical” flaw in Intel’s hardware. Reporting less severe bugs is still worth the effort, ranging in value from $500 to $1,000, according to the company’s newly rolled out bug bounty program website.
“We want to encourage researchers to identify issues and bring them to us directly so that we can take prompt steps to evaluate and correct them, and we want to recognize researchers for the work that they put in when researching a vulnerability,” Intel said March 15. By partnering constructively with the security research community, we believe we will be better able to protect our customers.”
Intel wants hackers to look closely at its software, hardware and firmware. The harder a bug is to fix, the more the company will pay:
Not all Intel products are eligible for this bug hunt. For example, McAfee products are excluded, and so are third party and open source products. Intel’s web infrastructure is also off limits for the bug bounty program, as are recent acquisitions (6 months after the acquisition is done).
You can find more details on HackerOne, a vulnerability coordination and bug bounty platform, which also hosted the “Hack the Pentagon" program, in which 138 unique bugs were discovered and mitigated. After that program’s success, the U.S. Army followed suit with its own version, “Hack the Army,” where hackers collected a total of over $100,000 in bounty.
Happy hunting!



